Have you ever wondered what happens behind the scenes when Deadbolt ransomware strikes? Understanding how this dangerous malware works can protect your files and save you from a costly nightmare.
You’ll learn exactly how Deadbolt ransomware infects your system, locks your data, and demands payment. Knowing these details puts you in control and helps you spot the warning signs before it’s too late. Keep reading to uncover the secrets of Deadbolt ransomware and find out how to keep your digital life safe.

Credit: www.acronis.com
Deadbolt Ransomware Origins
Deadbolt ransomware has caught attention due to its harmful impact. Understanding its origins helps to grasp the threat it poses. This ransomware first appeared with unique features that set it apart from others.
Its development shows growing sophistication in cybercrime. The journey of Deadbolt reveals insights into how ransomware evolves and targets victims.
Initial Discovery
Deadbolt ransomware was first spotted in early 2022. Security experts noticed it after attacks on several online services. The ransomware quickly gained a reputation for targeting specific systems. Early samples showed a new way to encrypt files and demand payment.
Targeted Platforms
Deadbolt mainly attacks NAS devices and cloud storage platforms. These platforms are popular among businesses and home users. By focusing on these, attackers maximize damage and payment chances. The ransomware locks users out of their own data, causing major disruption.
Attackers Behind Deadbolt
The group behind Deadbolt remains largely unknown. They use advanced techniques to hide their identity. Their goal is financial gain through ransom payments. This group adapts quickly, making it harder for defenders to stop them.

Credit: www.fortinet.com
Infection Methods
Deadbolt ransomware spreads through several infection methods. These methods help the malware enter devices and start encrypting files. Knowing these ways helps protect your data and devices.
Phishing Emails
Phishing emails trick users into clicking dangerous links or attachments. These emails look real but hide harmful software. Once clicked, Deadbolt ransomware installs silently on the device.
Attackers use fake messages from trusted sources. They create urgency or fear to make people act fast. This method is common and very effective.
Exploiting Vulnerabilities
Deadbolt finds weak spots in software or devices. These weak spots are called vulnerabilities. Hackers use them to enter systems without permission.
Outdated software or missing security patches make devices easy targets. Once inside, ransomware spreads quickly and locks files.
Malicious Downloads
Downloading files from unsafe websites can bring Deadbolt ransomware. These downloads may look like useful apps or updates. But they contain harmful code.
Users unknowingly install ransomware by running these files. Always download from trusted sources only. This reduces the risk of infection.
Encryption Process
The encryption process is the core action of Deadbolt ransomware. It takes files on the infected system and locks them. This prevents users from opening or using their own data. The ransomware uses a careful method to find, encrypt, and lock files. Understanding this process helps to see how the attack works and why it is dangerous.
File Targeting
Deadbolt searches for specific file types on the computer. It looks for files that hold valuable information. These include documents, images, videos, and databases. The ransomware skips system files to keep the operating system running. It targets files most important to the user or business. This selective approach makes the attack more harmful.
Encryption Algorithms
The ransomware uses strong encryption algorithms to lock files. These algorithms scramble data into unreadable code. Deadbolt often uses AES or RSA encryption methods. AES encrypts files quickly and securely. RSA helps to protect the keys that unlock the files. Together, they create a tough lock that is hard to break.
Locking Mechanism
After encrypting, Deadbolt changes the file extensions. This shows the files are locked and unusable. The ransomware also creates a ransom note on the system. This note demands payment in exchange for the decryption key. Without the key, files remain locked and inaccessible. The locking mechanism forces victims to decide quickly.
Credit: www.thesslstore.com
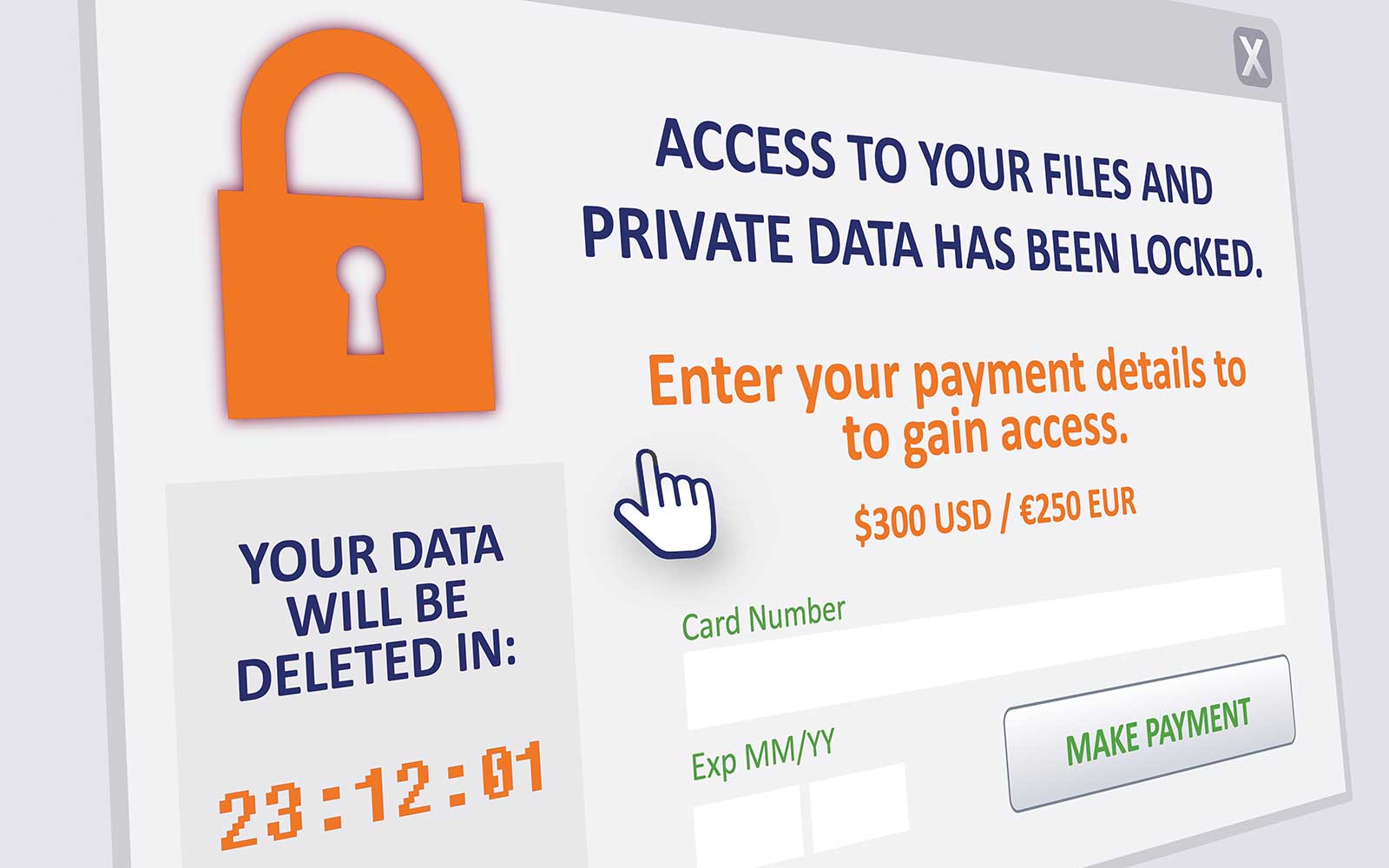
Ransom Demand Tactics
Deadbolt ransomware uses specific tactics to demand money from victims. These methods guide victims on how to pay the ransom. The attackers want to make the process clear and urgent. This helps increase the chances that victims will comply quickly.
Ransom Note Delivery
After encrypting files, Deadbolt leaves a ransom note. This note appears on the victim’s screen or in affected folders. It explains what happened and what the victim must do next. The note often uses simple language to avoid confusion. It creates a sense of urgency to push for fast payment.
Payment Instructions
The ransom note includes detailed payment instructions. It tells victims which cryptocurrency to use, often Bitcoin. Wallet addresses are provided for sending the payment. The note may also list the ransom amount and deadlines. Clear steps reduce hesitation and help victims follow through.
Communication Channels
Deadbolt operators offer ways to communicate after payment demands. They might provide email addresses or chat links for contact. This lets victims ask questions or negotiate. Communication appears controlled but aims to keep victims engaged. It helps attackers maintain pressure and trust.
Impact On Victims
Deadbolt ransomware causes serious problems for victims. It locks important files and demands money to release them. The effects go beyond just losing access to data. Businesses and individuals face many challenges that can harm their work and finances.
Understanding the impact helps prepare for possible attacks. It shows why strong security is necessary. The damage from Deadbolt can last a long time.
Data Loss Risks
Deadbolt encrypts files, making them unreadable. Victims lose access to personal and business data. Backups may also get infected or deleted. Without backups, data recovery is very hard. Some files might be lost forever. This can affect future projects and records.
Operational Disruptions
Work slows down or stops completely. Systems become unusable until files are decrypted. Employees cannot perform daily tasks. Customer service may suffer due to delays. Deadbolt causes downtime that impacts productivity. This disruption can damage reputation and trust.
Financial Consequences
Victims face ransom demands to regain data. Paying ransom does not guarantee file recovery. Costs include paying experts to fix systems. Lost business during downtime reduces income. Additional expenses come from security upgrades. Overall, financial losses can be very high.
Detection And Prevention
Deadbolt ransomware continues to evolve, posing greater risks. Attackers improve their tools and methods to bypass defenses. Understanding future threats helps protect systems better. Staying alert to changes is key for safety.
Emerging Variants
New versions of Deadbolt ransomware appear frequently. Each variant may use different code or tricks. Some target specific devices or networks. This variety makes detection harder for security tools. Watching these variants helps prepare defenses early.
Changing Tactics
Attackers alter how they deliver ransomware. They may use phishing emails or weak system gaps. Some avoid detection by hiding payloads carefully. Others demand higher ransoms or threaten data leaks. These changes force security teams to adapt fast.
Staying Ahead
Regular software updates reduce risks of infection. Backup data often to recover from attacks quickly. Educate users about suspicious emails and links. Use strong passwords and multi-factor authentication. Combining these steps keeps systems safer against Deadbolt threats.
Frequently Asked Questions
What Is Deadbolt Ransomware And How Does It Spread?
Deadbolt ransomware is a malware that encrypts files and demands payment. It spreads mainly through phishing emails and unsecured Remote Desktop Protocols (RDP).
How Does Deadbolt Ransomware Encrypt Victim Files?
Deadbolt uses strong encryption algorithms to lock files. It targets important data and makes it inaccessible without a decryption key.
Can Deadbolt Ransomware Be Removed Without Paying Ransom?
Yes, removal tools can delete the ransomware, but file recovery is hard without backups or decryptors. Prevention is crucial.
What Are Common Signs Of Deadbolt Ransomware Infection?
Signs include locked files, ransom notes demanding payment, slow system performance, and inaccessible data.
Conclusion
Deadbolt ransomware targets files and demands payment for access. It spreads through email attachments and unsafe downloads. Once inside, it locks important data quickly. Users must stay alert and avoid suspicious links. Regular backups help protect against data loss. Keeping software updated blocks many threats.
Understanding how Deadbolt works helps users stay safe. Prevention is always better than dealing with attacks. Stay cautious and protect your digital life.


